With the surge of technology in consumerism, it is no surprise that e-waste is the fastest growing type of waste on the planet right now. E-waste still has valuable information which can be extracted and cause you or your potential company damage. There is also the threat that e-waste has on the environment if not correctly disposed of. To protect yourself, your company, as well as the environment, be sure to follow three simple rules to recycle your electronic waste.
.jpeg)
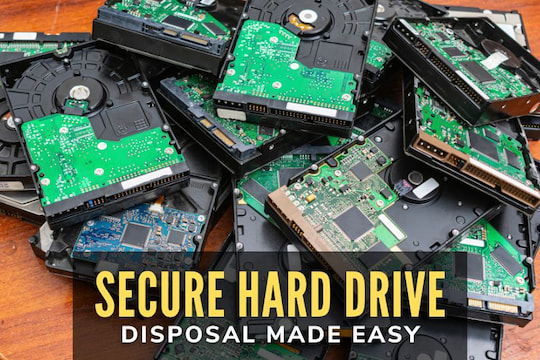
The first rule is to do some research on your recycler. It is essential to gather as much information as to where to recycle e-waste because each recycling company is different. Despite the growing number of e-waste companies, there are only a few you should be looking at. You must make sure R2 Solutions or e-Stewards certify the company you choose. This will ensure that your e-waste is recycled adequately so that no harm comes to the environment and that all of your data will remain private. These standards also provide that there is accountability throughout the disposition process. Avoid companies that say they will work with certified recyclers eventually or later in their process because it leaves your information not adequately protected.
The second rule is to realize that if it’s too good to be true, it probably is. Although you will find many “free” recycling services, if you want things done right, you will have to pay for it. When you use “free” services, you will likely run into two risks. The first risk imposes the possibility of the company likely cutting corners, resulting in harm to the environment. The second risk may be that the company can even sell your equipment – along with all your information – to the highest bidder. Either situation is one that should be avoided.
The third and final rule to follow is to create a formal plan for disposition and make sure to support it. In February of this year, the National Institute of Standards and Technology issued a new Cybersecurity Framework that established the best ways to ensure data security. They strongly suggest for all assets to be “formally managed throughout the removal, transfers, and disposition.” When creating your data security plan, make sure that it includes a rule that mandates the use of certified recyclers for all your electronic and IT asset disposition. This will be a surefire way to keep your company safe from stolen information while doing your part to keep the environment clean.





.jpg)