Securing your sensitive information encompasses practicing safe internet browsing habits and running a quality antivirus program on your business and personal computers, whether they are desktops or laptops. Now, failing to recognize the vulnerabilities posed by the vast quantity of internet-connected devices can leave you trying to play catch up.
The phrase Internet of Things (IoT) has been coined to better describe what used to be the purview of just computers. Everything from the refrigerator in your employee break room to your company vehicles and even the coffee maker can likely be connected to the internet, and anything with an internet connection is a potential threat vector. Managing IoT device security vulnerabilities can be a full-time job, so we've compiled some best practices to help ensure your enterprise is better protected.
Securing Your Devices
Install Patches and Updates

Probably the most effective step you can take when addressing IoT device security vulnerabilities is to ensure that any connected devices are regularly scanning for and installing updates and patches. As the manufacturer or developer discovers and addresses bugs or security vulnerabilities, they push out fixes for them in software and operating system updates. Failing to check for and install available updates is the single biggest cause of device compromise.
Utilize Encryption and Require Credentialed Access

Secondly, install passwords and encryption on any device that will accept it. This doesn't help manage your WiFi-capable office thermostat, but this step can prove invaluable for tablets, e-readers, cell phones, and other similar devices. You should also discourage using the same password for multiple devices or user accounts. This helps to protect you from the loss or theft of a device, leading to a more devastating compromise of your business systems by protecting the data on the device behind a password and encryption.
Monitor Network Traffic

Any of these steps are better than being unprepared, but the reality is that you can't fully protect any device or network. You should invest in a robust scanning tool to monitor network access and verify that the behavior of all connected devices is appropriate. If suspicious or outright malicious activity is discovered, the program should escalate that alert to the appropriate IT personnel for review and response. This leads us to our next point, which is that you can't monitor what you aren't aware of.
Keeps Tabs on All IoT Devices
We also recommend recording and logging all IoT devices on a spreadsheet. This is helpful for accountability purposes and allows you to revisit their necessity as a part of your regular risk assessment process. If a device isn't being used or is proving to be inferior to another non-internet-connected device, then you may be better off shifting away from that device entirely.
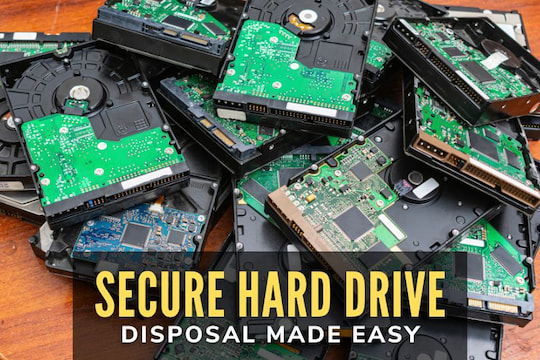
Plan for End of Lifecycle
This brings us to our next item, which is the most overlooked of all, at least in our experience. When a device reaches the end of its lifecycle or is broken, how are you disposing of it? Do you just toss it in the trash and try to put it out of your mind? That's a gift for a cyber attacker with the funds to pay someone to sift through your garbage or the patience to do it themselves.
Having data destruction procedures and a device decommissioning process can prove invaluable when trying to mitigate IoT device security vulnerabilities. Scrubbing devices of any sensitive data is a must, and professional computer recyclers have the tools and the knowledge to make sure that you're keeping all usable data.