In this world of fast-paced technology, it seems like there is always a new cyber threat that companies need to be aware of. While there are several ways to protect your company’s sensitive information against cyber attacks, you might also want some data security advice specifically about what happens at the end of an electronic equipment’s life cycle. Read on to learn more about the importance of data destruction when it comes to data security.
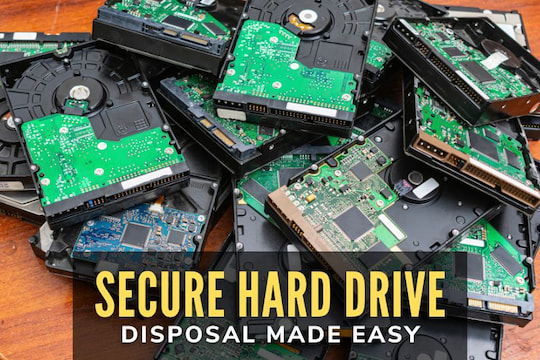
One of the first things that your company will want to do is to create a company-wide procedure for data destruction. Data destruction is essential because all forms of data remain on the hard drive of a computer or device even after the files have been deleted. If the physical piece of equipment gets into the wrong hands, your company may be at risk of a security breach. In the world of data security, the best offense is a good defense, and the way to defend against a breach is by first creating a plan. When it comes to your data destruction policy, you’ll want to determine everything in your company that may require data destruction such as hard drives from computers, servers on the company LAN, portable storage devices such as USB drives and even phones. Once a list is compiled, determine where the devices will go once they are retired. The best way to keep your data secure is through the physical destruction of these devices via a third party data destruction company.
Once the plan is in place, it is imperative that all staff are informed about the policy as well as being informed about the importance of data destruction. Let them know that devices such as copy machines, printers, mobile phones, tablets, and USB drives can all be potential security breaches. As a result, they should never be thrown away. Finally, once a device is retired, be sure to acquire documentation that the data has been destroyed. Only hire a third party company that will provide a certificate of destruction. This certificate will often include information such as the type of device that was destroyed as well as the serial number of the hard drive or the storage device that was destroyed. These are some simple guidelines to follow to achieve best practices when it comes to data security.