It’s no surprise that cybersecurity is a hot topic in today’s world. There are regular reports of large companies’ private systems being hacked into, resulting in many individuals’ personal information being stolen. This can be worrisome to hear because one would think that these large companies spend a ton of money trying to keep their systems secure to prevent this from happening.
In response to all of the latest hacking incidents, the House of Representatives has recently passed a new bill titled the Protecting Cyber Networks Act. Essentially, this bill will allow corporations to share your data with other corporations and with the federal government. The government is hoping that by allowing federal investigators this access, they will be able to prevent future attacks and catch the initial culprits. There has been some backlash by the public regarding this bill for a few reasons. First, it involves the sharing of personal data with both other corporations and the government. Second, many believe that the legislation is written vaguely and that it grants the government access to use the data they find in their investigation outside the scope of the cyber attack. The House and Senate still need to come together for final legislation of the bill.
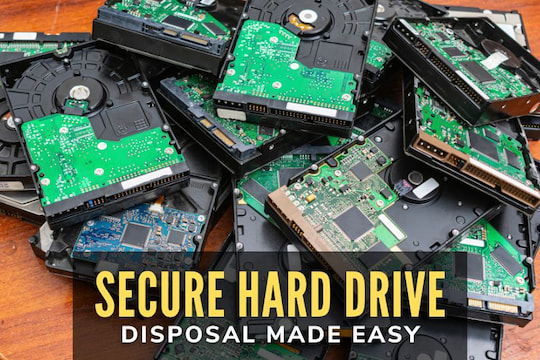
It can indeed be devastating to have your identity stolen. If your personal information gets into the wrong hands, not only can your credit potentially be ruined, but it can also take months and even years to get everything all sorted out. This can delay plans you have to buy a house, buy a car, or even take out a loan. One step you can take to protect your identity is to monitor your credit every so often. If you hear of a significant security breach, such as the recent one with Target, you may want to check your credit an additional time to make sure you were not a victim. A second step you can take, that most people don’t often think of, is taking the time to make sure you properly destroy electronics that contain personal and sensitive data, such as computers. By taking these two steps, you are protecting yourself and will hopefully catch any identity theft early on.